Ever had the experience of annoying ads following you around, from one site to another, based on your purchases or page views on Amazon? That process is done through automated tracking of your data as you browse the web.
Now, imagine a system that could conduct this activity across social media platforms, using nothing more than your face and name. This concept is what the company, TrustWave, has developed into a new tool called Social Mapper.
Social Mapper is open-source, equipped with facial recognition and can find your social media profile, using just a picture. Inventors of the product insist that it exists for the purposes of security research, but it could lead to other, less noble applications.
Model of Social Media Tracking
TrustWave is a group of cybersecurity experts and ‘ethical hackers’ that evaluate the vulnerability of various areas of the internet by ‘modeling’ hacks and other exploits.
The company has recently turned its efforts to the problem of social media-based phishing. This style of online attack may be based on gathering information about the entire social presence of an individual. In other words, potential hackers go through all the social sites (e.g., Facebook, LinkedIn) for a name, picture, or both, matching their reference material. On the other hand, this is time-consuming and complicated manual e-labor.
However, TrustWave has solved this problem by developing Social Mapper. This app performs the same type of searches, which requires no more information than a name and profile portrait shot, independently.
Social Mapper uses an instrumented window in a conventional browser for these searches. Therefore, it does not require API access to the social media platforms. The revocation of this access, in the past, has stopped similar tools such as Geofeedia.
Social Mapper requires a name search and then applies facial recognition to the first 10 to 20 results. It does this based on input such as CSV files, image folders or common search terms. Social Mapper expresses positive hits as a spreadsheet with all the confirmed profiles per name and face.
However, this makes the process very slow, especially compared to the abilities of API-based tools. TrustWave estimates that it could only process a maximum of 66.67 people by the hour.

Social Mapper correlates one image on a social media site with that on another to match profiles to a single name. (Source: U.S. Air Force by Airman 1st Class Erin R. Babis/Released)
How Social Mapper Can Be Exploited
The resulting list of profiles per target may make a perfect resource for a phishing attack or other forms of online malfeasance. However, TrustWave asserted that they intend Social Mapper to be used for purposes such as ‘white hat’ or ethical hacking only.
On the other hand, the company can no longer be in control of its uses and applications. Social Mapper was also made open-source, and it is available on GitHub to virtually anyone who wants it. Conversely, it is listing on this resource targets security researchers and developers.
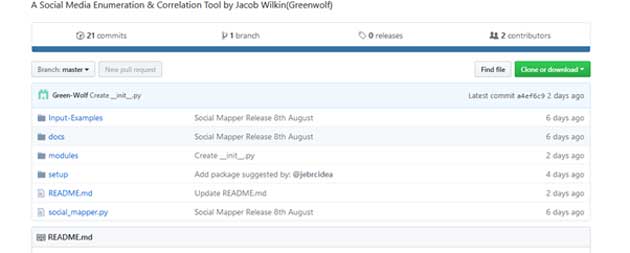
Social Mapper’s downloads on GitHub. (Source: Author’s own work)
TrustWave suggested that these users run Social Mapper to evaluate susceptibility to phishing and intrusion, emanating from social media, within their organizations (or outside it).
On the GitHub page, the developers also noted that individuals were now more likely to click a link (that could point to malware) sent to them via social media compared to links sent in emails.
The company went as far as to suggest that those who use Social Mapper could launch false voucher campaigns in order to capture personal data or familiarize themselves with the target’s typical surroundings (e.g., their workplace) through the backgrounds of photos.
Social Mapper was built to be compatible with many popular social media platforms, including Twitter, Facebook, and Instagram. The app can also target slightly more region-specific sites such as Weibo or Douban.
TrustWave also believed that Social Mapper should run on systems such as Windows and Linux, using Firefox, Geckodriver, and Selenium. Presently, it is based on Python and requires credentials to log into social media sites. Assuming that these requirements pan out, it may then be free to find all the profiles needed by users.
Is There a Response to Social Media Tracking?
Tools such as Social Mapper indicate the worrying efficiency with which malicious code and strategies improve in terms of sophistication and, possibly, more importantly, automation. On the other hand, if attack-focused software moves this fast, maybe the counterparts that can block or disable it can too.
Top Image: Social media is a rich source of faces, names, and the potential targets behind them. (Source: Pixabay)
References
New facial recognition tool tracks targets across different social networks, The Verge, https://www.theverge.com/2018/8/8/17663640/socialmapper-facial-recognition-open-source-intelligence , (accessed 13 Aug. 18)
A Social Media Enumeration & Correlation Tool by Jacob Wilkin(Greenwolf), 2018, Social Mapper GitHub, https://github.com/SpiderLabs/social_mapper , (accessed on 13 Aug. 18)
Can Facebook and Twitter stop social media surveillance?, 2018, The Verge, https://www.theverge.com/2016/10/12/13257080/police-surveillance-facebook-twitter-instagram-geofeedia , (accessed 13 Aug. 18)







No comment